Browser-native vs cloud bots: what actually works on protected storefronts in 2026
Most buyers pick a tool based on reputation or price. The ones who execute consistently pick based on architecture. Cloud bots and browser-native tools are not just different implementations of the same idea—they operate in fundamentally different security environments. Understanding the difference tells you exactly why one type of tool is losing reliability and the other is gaining it.
Retailer security has matured significantly since 2023. Target, Pop Mart, Nike, and a growing subset of Shopify stores now deploy behavioral analysis that fingerprints sessions at a level far beyond simple IP reputation. The tools that were reliable two years ago on these storefronts are producing declining results—not because the tools changed, but because the detection surface they operate on has expanded. This article breaks down what that detection surface actually looks like and what a browser-native approach does differently.
1. What a cloud bot actually is—and where it breaks down
The phrase "cloud bot" covers a wide range of architectures, but they share a common trait: execution happens on a remote server, not inside your local browser. The tool communicates with retailer servers either through direct API calls or through a headless browser environment—a browser that renders pages without a visible window, typically Chromium running via Puppeteer, Playwright, or a similar driver.
The detection problem is architectural, not implementation-specific. Even the most sophisticated headless browser environment produces a measurably different signal set than a real browser running on a physical machine:
- TLS fingerprint: Real Chrome on a user's machine produces a distinctive TLS ClientHello fingerprint based on cipher suite ordering and extension set. Headless Chromium and server-side request libraries produce different fingerprints that are catalogued by security systems.
- Rendering signals: A real browser generates continual rendering events—paint timing, layout shifts, media decoding signals, and font rendering metrics. Headless environments either suppress these or produce them at statistically improbable intervals.
- WebGL and canvas fingerprinting: GPU-rendered canvas operations produce hardware-specific outputs. Headless environments typically use software rendering or report virtualized GPU information that does not match the claimed user agent.
- Behavioral chain coherence: Real users scroll, hover, and pause before clicking. Sessions that jump directly from page load to add-to-cart with no intermediate events fail behavioral coherence models used by Shape, Akamai, and Shopify's bot management stack.
2. What a browser-native tool is—and why the distinction matters
A browser-native execution tool runs directly inside a real, headed browser—the same Chrome instance running on your machine with a GPU, a display stack, and real hardware fingerprints. The tool interacts with the browser through its extension layer rather than through external API calls or driver protocols.
This distinction matters because the security signals that behavioral analysis systems measure are produced by the browser itself, not by the tool. When Vectorcart executes a cart action inside Chrome, it is using the same event dispatch system that your mouse click would use. The TLS handshake is Chrome's. The rendering signals are Chrome's. The canvas fingerprint is your GPU's.
From the retailer's perspective—and from the perspective of Shape Security or Shopify's bot management layer—the session is a Chrome session. Because it is one.
3. The security layers each architecture faces: a retailer-by-retailer breakdown
Not every retailer deploys the same protection stack. Understanding what each major protected storefront uses clarifies which architecture is required for reliable execution.
- Target (Shape Security / F5): Analyzes behavioral chain consistency, TLS fingerprint, session cookie coherence, and IP reputation in combination. Shape's detection rate on headless Chromium—even with stealth patches—has increased materially since 2024. Browser-native execution is the established reliable path on Shape-protected endpoints.
- Pop Mart: Uses behavioral analysis with device fingerprinting emphasis. High block rates on headless sessions were documented through 2025, particularly on the PopNow instant-buy module where session warmup and rendering history are scored. Vectorcart's Core Certified status on Pop Mart was established through browser-native execution in March 2026.
- Nike (Akamai Bot Manager): One of the most actively maintained detection systems in the space. Akamai uses sensor-based telemetry collection that runs in-browser JavaScript to collect hundreds of behavioral and hardware signals throughout the session. Cloud tools that attempt to inject fake sensor data are detected through statistical inconsistency in the telemetry stream. A real browser produces real telemetry because the hardware and interaction events are genuine.
- Shopify (Bot Protection, Managed Challenge): Shopify's protection varies significantly by store. Stores using Shopify's native Bot Protection or third-party apps like Kasada face similar detection profiles to the above. API-based checkout routes were largely closed for bot usage in 2023–2024 through Shopify's payment security updates. Browser-native checkout through the storefront remains the cleaner execution path on protected stores.
- GameStop, Best Buy: Generally lighter protection profiles compared to Target or Nike. Cloud tools retain higher success rates here, though browser-native execution produces fewer edge-case failures during high-traffic events when server-side defenses are temporarily elevated.
4. Where cloud bots still have a real advantage
A technically honest comparison requires acknowledging where cloud architecture has structural advantages that browser-native tools do not replicate easily.
- Scale: Cloud bots can spin up hundreds or thousands of concurrent sessions on server infrastructure. Browser-native tools are bounded by the number of browser tabs that can run on a local machine. For operations running at very high concurrency, cloud architecture is the only viable execution model—on storefronts where it can still operate reliably.
- Latency: Cloud bots hosted in data centers geographically close to retailer servers can achieve lower network latency than a local residential connection. This advantage is real but narrow: checkout and add-to-cart speed differences at the millisecond level are less determinative than detection-layer pass/fail outcomes.
- Unattended operation: Cloud bots can run continuously without a local machine staying online. Browser-native tools require the local machine and browser to be active. This is a legitimate operational constraint for buyers who want background execution without maintaining an active session.
- Lightly protected storefronts: On retailers with minimal bot detection—some smaller Shopify stores, certain specialty retailers—cloud tools operate without friction. The detection problem only matters where behavioral analysis is actively deployed.
5. The hybrid architecture: how Vectorcart combines both layers
Vectorcart is not purely a local execution tool—it is a two-layer system. Understanding both layers clarifies what each handles and why the architecture was designed this way.
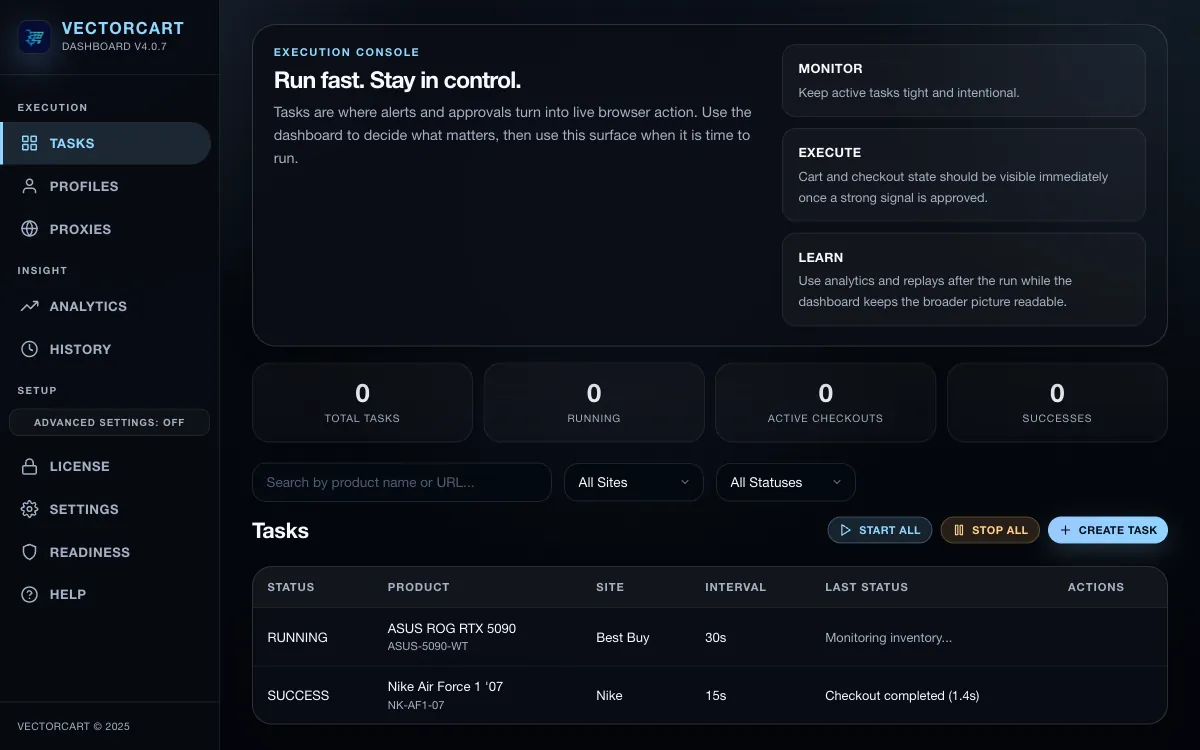
- Execution layer (browser extension): The Chrome extension handles all direct retailer interactions—monitoring, product page navigation, add-to-cart, and checkout. These actions run in a real headed browser tab with real hardware and session signals. This is the layer that produces the detection-safe execution profile.
- Control layer (Vectorcart.app dashboard): The dashboard handles orchestration, queue policy, proxy assignment, alerts, approvals, ACE (Adaptive Checkout Intelligence) decisions, replay history, and task management. This layer does not interact with retailers directly—it coordinates the execution layer and provides the visibility and control surface for managing complex workflows.
This separation means the detection-sensitive work stays in the browser, where it produces authentic signals, while the orchestration overhead runs in the cloud where it is not exposed to retailer security scrutiny. Neither layer alone is the full system.
6. Practical decision framework: which approach fits your workflow
The right tool depends on where you are running, what volume you need, and how the retailer's protection stack is configured. Use this framework to make an evidence-based decision rather than a reputation-based one.
- Shape-protected storefronts (Target, Pop Mart): Browser-native execution is the consistent path. Cloud tools face structural challenges here that stealth patches and proxy rotation cannot fully resolve.
- Akamai-protected storefronts (Nike): Browser-native execution removes the sensor telemetry authenticity problem entirely. Real browser hardware produces real signals—this is the architecture advantage, not a feature.
- Shopify stores with active bot protection: Browser-native is the reliable path. Shopify's API-based checkout routes have been progressively closed for automation since 2023.
- Lightly protected storefronts at high concurrency: Cloud bots retain an advantage at scale. If the storefront has no meaningful behavioral analysis and you need hundreds of concurrent sessions, cloud architecture is appropriate.
- Mixed portfolio (multiple retailers, multiple protection levels): A browser-native tool with dashboard orchestration like Vectorcart covers the high-detection retailers reliably while remaining capable on lower-protection lanes. This avoids maintaining separate tool stacks for different retailer types.
7. What to look for when evaluating any execution tool in 2026
Marketing claims from bot tools are difficult to verify without running the tool yourself. These are the practical questions that cut through marketing language and reveal actual architectural capability.
- Does it run in a headed or headless browser? If the answer is headless, or if the tool does not disclose its browser environment, assume headless detection risks apply on Shape and Akamai storefronts.
- Does it support proxy binding at the session level? Per-session proxy binding is essential for multi-account execution. Tools that rotate proxies mid-session introduce session coherence failures on behavioral analysis systems.
- Is there logged proof of execution? Replay logs, history, and stage-level failure classification are the evidence layer that separates a tool making claims from a tool producing verifiable results.
- What is the update cadence when detection changes? Detection systems are updated continuously. A tool without an active development team responding to detection changes will degrade in reliability over time regardless of its current performance.
- Does the tool disclose its support tiers explicitly? Any tool claiming support for every retailer without qualification is overstating. Honest tools publish what they have tested and verified, with explicit notes on where account-state or headed browser behavior is required.
8. Frequently asked questions: browser-native vs cloud bots
What is a browser-native bot?
A browser-native execution tool operates inside a real, headed browser—typically Chrome. It interacts with pages using the full browser engine stack, so its session signals, fingerprints, and behavioral patterns are those of a real browser, not a simulated one.
What is a cloud bot and how is it different?
A cloud bot runs on remote servers using headless browsers or API calls. Because these environments lack a full graphical rendering stack, they produce fingerprint differences that modern behavioral analysis systems—Shape, Akamai, Shopify Bot Protection—use to classify and block sessions.
Are cloud bots completely obsolete in 2026?
No. Cloud bots remain effective on storefronts with minimal bot protection and offer real scale advantages at high concurrency. The decline is specific to retailers that have deployed mature behavioral analysis like Shape Security, Akamai Bot Manager, and Shopify's current protection stack.
Which retailers specifically require browser-native execution?
Target (Shape Security), Pop Mart, Nike (Akamai), and Shopify stores using advanced bot protection have the highest headless detection rates in 2026. Browser-native execution produces materially better checkout-stage outcomes on these storefronts.
Is Vectorcart a browser-native tool?
Yes. Vectorcart's v5.0 execution layer operates directly inside a headed Chrome tab. The extension handles monitoring, carting, and checkout in the real browser. Vectorcart.app is the control layer for orchestration, queue policy, ACE decisions, and replay—it does not interact with retailers directly.
Does this mean Vectorcart guarantees successful checkouts?
No. Browser-native execution removes a class of detection-based failures. Actual checkout outcomes also depend on account state, proxy quality, inventory availability, and retailer behavior at the moment of execution. See our Terms for the full scope.
